Iran-linked hackers disrupt Stryker by triggering remote device wipes
NBC reports Intune console access used to reset corporate phones, civilian healthcare supply chains absorb the shock
Images
 nbcnews.com
nbcnews.com
 Stryker, based in Michigan, produces a range of medical equipment and technology.Smith Collection / Gado via Getty Images file
nbcnews.com
Stryker, based in Michigan, produces a range of medical equipment and technology.Smith Collection / Gado via Getty Images file
nbcnews.com
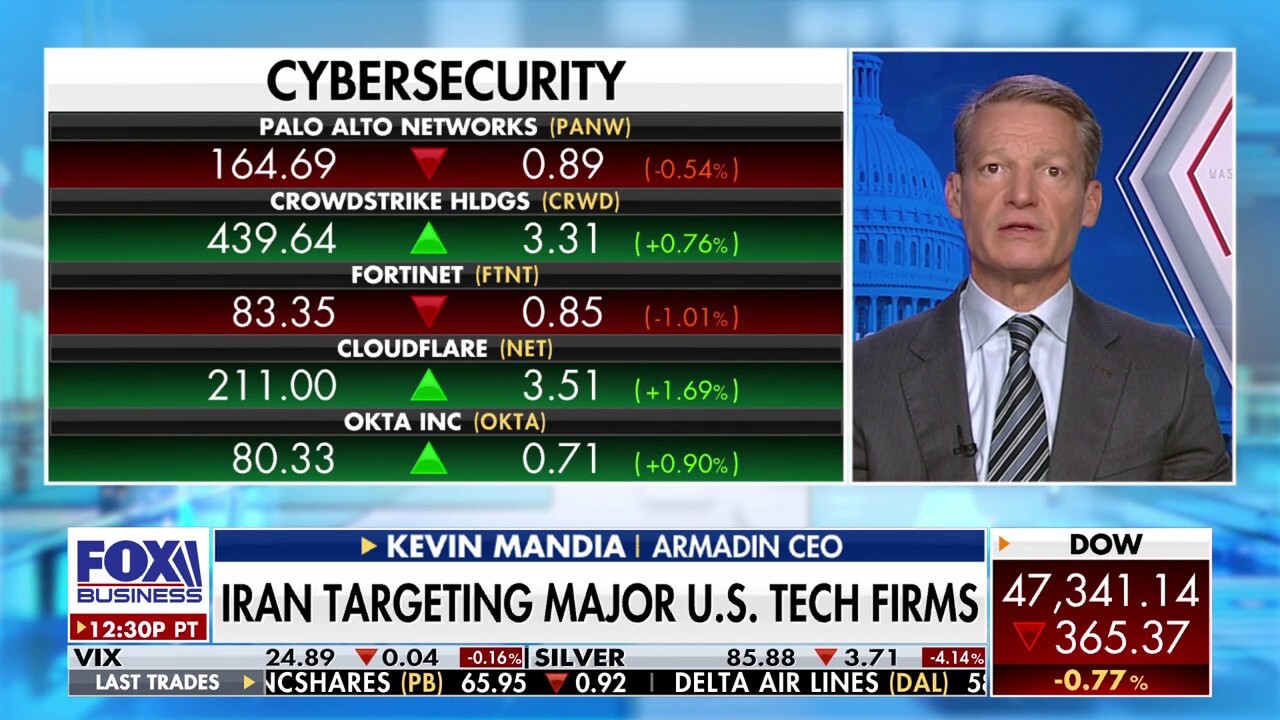 Armadin CEO Kevin Mandia discusses Iran's escalation from threatening ships to allegedly targeting American companies like Stryker and major U.S. tech firms with cyberattacks on 'The Claman Countdown.'
foxbusiness.com
Armadin CEO Kevin Mandia discusses Iran's escalation from threatening ships to allegedly targeting American companies like Stryker and major U.S. tech firms with cyberattacks on 'The Claman Countdown.'
foxbusiness.com
 Cyber security IT engineer working on protecting network against cyberattack from hackers on internet.
foxbusiness.com
Cyber security IT engineer working on protecting network against cyberattack from hackers on internet.
foxbusiness.com
 cyber attack
foxbusiness.com
cyber attack
foxbusiness.com
 hacking victim
foxbusiness.com
hacking victim
foxbusiness.com
Iran-linked hackers appear to have disrupted medical device maker Stryker by abusing Microsoft Intune’s remote wipe capabilities, knocking employee phones offline and disrupting communications, according to NBC News. The group “Handala Team” claimed responsibility on Telegram and X, while Stryker said it was experiencing a “global network disruption” in its Microsoft environment, believed the incident was contained, and saw no indication of ransomware or malware.
The mechanics described by cybersecurity researchers point to a specific kind of attack that fits the current phase of the war: not stealing money, not negotiating for decryption keys, but using corporate management tools to erase devices at scale. Intune exists so companies can wipe lost phones; if an attacker gets access to the management console, the same feature becomes a weapon. That shifts the centre of gravity from perimeter hacking to identity, permissions, and administrative consoles—the places where modern organisations concentrate power for efficiency.
Handala has been linked by Sophos to Iran’s Intelligence Ministry, NBC reports, but the group presents itself as “hacktivist,” a label that helps everyone involved. Tehran gains plausible deniability while still signalling capability; the group gains a political brand that makes deterrence difficult because it is not primarily profit-driven; and targeted firms are left describing “disruption” without immediately attributing it to a state actor. In practice, the result is that civilian infrastructure becomes the easiest place to impose costs without crossing the clearer red lines associated with kinetic attacks.
Stryker sits in an uncomfortable category: a civilian supplier whose products are embedded in hospitals and emergency care, but also a contractor ecosystem that touches defence procurement. Disrupting internal communications and managed devices does not need to breach factory control systems to create real-world consequences—delayed service calls, postponed installations, and slower support for clinics that rely on vendor coordination. Those downstream costs are borne by patients and healthcare staff long before they appear in quarterly filings.
The episode also illustrates why “contained” can be a narrow statement. If the attacker’s access is to the device-management layer rather than core servers, the organisation can truthfully say its internal systems were not directly hacked while still losing the ability to operate normally. What looks like a technical incident becomes a governance question: who can issue wipes, how those permissions are audited, and how quickly a global enterprise can re-enrol thousands of devices when the control plane is the target.
Stryker said it had no indication of ransomware. Employees described wiped work phones and stalled communications.
